BYOD SECURITY MARKET REPORT SCOPE & OVERVIEW:
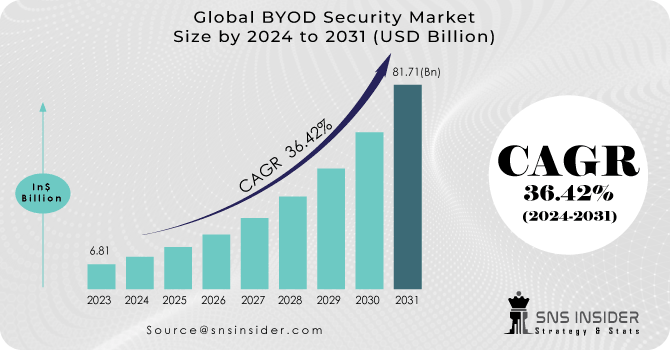
The BYOD Security Market was valued at USD 61.5 billion in 2023 and is expected to reach USD 209.19 billion by 2032, growing at a CAGR of 14.61% over the forecast period 2024-2032.
The growth of the BYOD (Bring Your Own Device) security market reflects the increasing prominence of remote and hybrid work models, wherein employees access corporate resources through their devices. It has been accelerated by COVID-19 and the trend for mobile workforces. With the advancement of digital transformation, mobile device security has become a means by which organizations can minimize the risks of data breaches, cyberattacks, and compliance issues. The need for advanced BYOD security solutions is driven further by the enterprise's expectations around securing critical data and compliance with data protection regulations such as GDPR & CCPA. More than 90% of remote employees utilize their devices, such as smartphones or tablets, to access work, but 32% operate unapproved applications, which can put organizations at risk. Nearly 45% of employees use the same password for work and personal accounts, making them more susceptible to data breaches. Moreover, 60% of corporate data is now stored in the cloud available on BYOD and requires better security. Top-level managers favor hybrid work adoption at 82% and businesses save up to USD 11,000 each year for each employee by allowing them to work from home.
Get More Information on BYOD Security Market - Request Sample Report
Moreover, the proliferation of smartphones and tablets and an increase in the use of mobile applications for business processes increases the growth rate of the market. With the scalability, flexibility, and cost-effectiveness provided by cloud-based solutions, organizations are becoming more reliant on them, progressively adopting BYOD security solutions such as Mobile Device Management (MDM) and Mobile Application Management (MAM) solutions. This demand is especially coming from SMEs who are looking for cost-effective and efficient security solutions, meanwhile, huge enterprises are still spending on advanced security infrastructure. This is boosted by the rising realization of mobile cybersecurity threats and securing any personal device used where you work in expectation of mobile enterprise growth. At least 75% of employees are anticipated to use personal gadgets for work by 2030 and 70% of world 5G-ready wearable gadgets will be adopted in North America and Asia Pacific. Companies adopting BYOD policies save USD 1,300 per employee, per year, and by 2032, 80% of BYOD solutions will be in the cloud. Companies are expected to boost acclaim on endpoint security a great deal, with enterprises to allot 25% of their IT budgets for cell phone security before 2028. Mobile business applications, in particular, are expected to expand at a rate of 34% per year.
MARKET DYNAMICS
KEY DRIVERS:
-
Rising Cyber Threats and Increased Attacks Fueling the Need for Strong BYOD Security Solutions
The increasing threat of cyber-attacks is one of the major factors driving the growth of the BYOD security market. However, with BYOD being adopted by more businesses, they are unintentionally exposing their networks to more and more potential vulnerabilities. Increased cyberattacks, ransomware, and phishing have caused enterprises to look for advanced security solutions to secure corporate and personal data on employee devices. Such personal devices often serve as an access route into corporate networks, and therefore protecting these devices is critical for organizations. As cyber threats become more sophisticated, organizations are adopting security measures such as Mobile Device Management (MDM) and Mobile Identity Management (MIM) to ensure that their data is protected over a range of devices. Such requirements for better security are fueling the BYOD security market and increasing end-user interest in real-time threat detection and protection solutions. In the second quarter of 2024, global cyberattacks rose 30%, exposing organizations to 1,636 attacks per week. The region of North America (58% of victims) followed the Industrial sector (56% increase in ransomware attacks.) Cyberattacks on the education sector increased 53% to an average of 3,341 weekly attacks and healthcare was attacked 1,999 times a week on average, up 15% year over year. Africa experienced the highest incidence of cyberattacks with a weekly average of 2,960, up 37% over the previous year. These escalating threats emphasize the importance of robust BYOD security solutions.
-
Leveraging AI and Machine Learning to Strengthen Security and Overcome BYOD Challenges in Organizations
A further key factor is the use of AI and machine learning technologies in BYOD security solutions. Security management technology needs to adapt smarter & faster based on the various types of diverse devices. Artificial intelligence and machine learning (AI/ML) are also able to analyze large datasets to identify anomalies and threats more quickly than traditional methods. It can be even more crucial in BYOD where the sheer volume and variety of devices accessing corporate networks makes manual tracking and safeguarding much more challenging. By incorporating AI-based fortifications, organizations are helped to rapidly resolve vulnerabilities and defend mobile hardware in real-time, thus providing a stronger barrier against growing cyber threats. Such technological advancements lead to rapid growth in the BYOD security market, as organizations are becoming aware of sophisticated security challenges. BYOD security is also being improved a lot with AI and machine learning technologies. 75% of cybersecurity professionals use AI for routine repetitive tasks, while 71% use it for monitoring traffic and detecting malware. In addition to that, 62% of organizations leverage AI/ML to forecast IT infrastructure weaknesses and the majority of professionals (64%) use artificial intelligence to identify phishing and malware attacks. These data points do show how the role of AI can emerge within the BYOD landscape, whether it is helping to improve threat detection, automating security processes, or predicting possible vulnerabilities.
RESTRAIN:
-
Managing Device Diversity and User Negligence in BYOD Security Remains a Major Challenge for Enterprises
One of the important constraints of the BYOD security market is the increasing complexity of managing a variety of devices and platforms. Employees are using everything from smartphones to laptops and tablets which can make it difficult for enterprises to apply uniform security protocols without affecting employee efficiency and productivity. Such fragmentation can complicate attempts at implementing end-to-end security, particularly if different components are running different operating systems, or if the devices have varying security capabilities. Managing a handful of device types makes it easier to uncover vulnerabilities than malware testing with hundreds of device types increasing room for oversight. A second problem is the negligence of the users themselves toward security protocols. Although organizations do have advanced security technologies, humans break security measures such as installing updates or using secure networks. Such behavior defeats the purpose of the security infrastructure and endangers corporate data. Securing Awareness while ensuring that employees are following best practices has been a major challenge for the majority of Operators adopting a BYOD policy.
KEY MARKET SEGMENTS
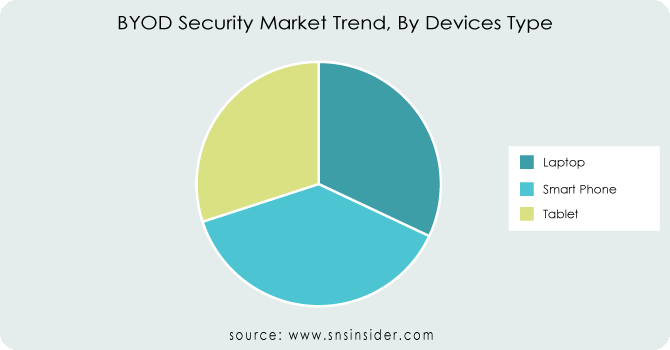
BY DEVICE TYPE
Laptops held the largest share of the BYOD security market at around 42.78% in 2023, because laptops are the primary device for many professionals across several sectors. Laptops are preferred because it has big screens, better processing power, and better multitasking features which make them profitable devices for productive work such as document creation, data analysis, communication, etc. Given that laptops are often the primary means of accessing enterprise networks, the demand to secure funds, protect company data, and ensure regulatory compliance increases exponentially.
Smartphones are projected to achieve the highest CAGR growth rate from 2024 to 2032 owing to a higher transition to a mobile-first work culture. With the use of mobile devices in day-to-day business operations, employees are relying on mobile phones for email and messaging, while also accessing company data and apps. This rapid adoption will come down to many things, particularly the increase in mobile apps and remote working. Advances in smartphone security solutions are expanding the market exponentially, driven by the increasing demand for flexible and always-connected work models. Also due to increasingly sophisticated processing and richer native enterprise-grade security features available on smartphones, organizations are adopting mobile-first altogether more and therefore, creating greater demand for more advanced BYOD security solutions for smartphones.
BY SOLUTION
The MDM (mobile device management) held the largest share of around 43.3% in 2023. MDM is a vital foundational solution for organizations that need to manage, secure, and monitor employee devices, as well as make sure that they comply with your corporate policies. As employee access is important to business data, and employees access their sensitive business data on their devices, MDM solutions protect these devices against security threats like unauthorized access, data leaks, malware, etc. MDM remains a critical layer of security, and enterprises continue to leverage it for security configurations, including device encryption, remote wipe, and secure app installations. MDM is thus, well ahead in the competition at large because a huge chunk of the market largely resides in the domain of high security and compliance-oriented industries like finance and healthcare.
Mobile Application Management (MAM) will account for the highest growth CAGRR during 2024–2032. This growth is driven by two major trends the rise of a mobile workforce and the growing use of mobile apps for work-related tasks. This is another point of difference in that MDM targets devices while MAM targets the apps themselves allowing for another layer of security around the corporate data inside the apps. With the usage of mobile apps to perform business functions like communications, collaboration, and data analysis growing, organizations are focusing more on mobile app security. Mobile Application Management (MAM) refers to the management of the use of corporate data within apps to ensure that it is not improperly used or misused, or data is not leaked from unauthorized use of apps by organizations. As mobile-first workflows become increasingly the norm, the need for MAM solutions will only increase as enterprises work to secure applications without sacrificing usability for mobile users.
BY DEPLOYMENT
The global BYOD security market is led by on-premises deployment, accounting for 56.2% market share in 2023. The reason is that many enterprises prefer more control over their data and security infrastructure, which is why it dominates. Solutions that are on-premise provide the benefit of hosting sensitive corporate data on the infrastructure of the organization itself, essential for industries that are highly regulated or follow strict data protection protocols such as finance, healthcare, and government. Furthermore, on-premises systems make it easier to integrate with existing enterprise systems and legacy technologies. These elements make on-premise the deployment of choice even in an era of accelerated cloud adoption.
The cloud-based solutions will register the highest CAGR growth between 2024 & 2032. These benefits make cloud-based BYOD security solutions an attractive option for businesses looking for flexibility, scalability, and cost efficiency. With the number of devices and users set to keep on growing, cloud platforms enable organizations to scale security quickly without requiring heavy capital costs on hardware or infrastructure. The centralized, 100 percent accessible, on-the-spot management and access of cloud solutions allow them to fulfill the remote work and mobile-first strategies. Cloud-based BYOD security solutions will see explosive growth in the coming years as companies look for more agile and cost-effective methods for securing their mobile workforce with the increasing use of cloud computing and the corresponding need for organizations to accommodate dispersed teams.
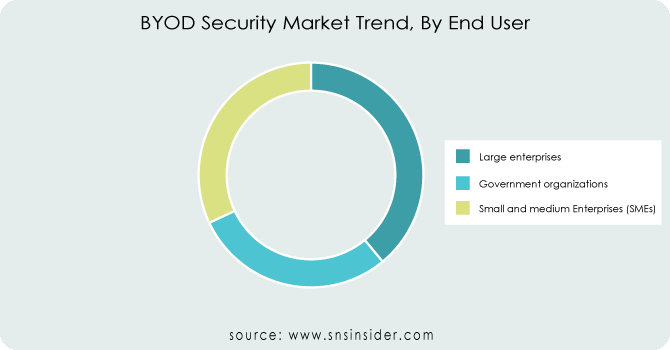
BY END USE
In 2023, large enterprises were the most significant shareholder in the BYOD security market with a market share of 47.8%. This is mainly because of the number of investments these organizations put into securing their IT infrastructure, especially, because a lot of devices and many users exist within their networks. For large enterprises, the scenario revolves around hundreds of devices accessing sensitive corporate data across complex, distributed environments, which calls for sophisticated security solutions such as Mobile Device Management (MDM), Mobile Application Management (MAM), and other advanced BYOD security solutions. Further, they face highly stringent regulatory and compliance obligations that increase the demand for security for their digital assets directly relating to business continuity as well.
The small and medium-sized enterprises (SMEs) segment is projected to be the fastest-growing segment in terms of CAGR during the period from 2024 to 2032. This growth has been primarily fueled by the increase in digitalization and the rising acceptance of remote working models. As mobile workforces grow, SMEs are beginning to see the value of BYOD security, with more employees accessing business data through personal devices. Despite the benefits, SMEs typically have fewer resources than large enterprises; therefore, cloud-based BYOD security solutions that are both scalable and cost-effective are particularly appealing. SMEs are expected to implement BYOD security solutions at an accelerated rate as there is a mounting need for mobile-first strategies and mobile applications are becoming central to business functions, thereby driving growth for this segment.
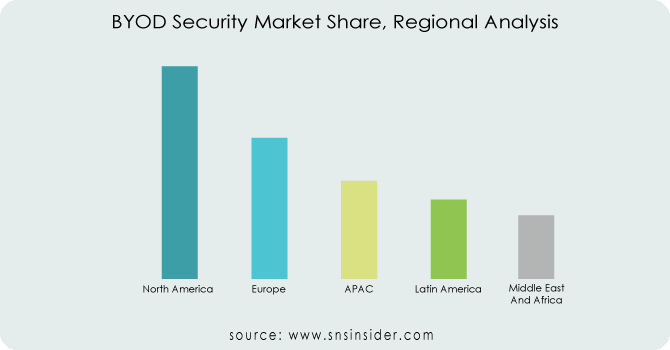
REGIONAL ANALYSIS
North America held a share of around 37.1% in the BYOD security market in 2023. Dominance is driven by the developed technology backbone, widespread internet access, and adoption of mobile-first and work-from-anywhere models across the region. Major Enterprises, Tech Market Players Protecting Sensitive Data with Mobile Security in North America. Alongside this, tighter data privacy regulations like GDPR in Europe and CCPA in California are pushing businesses in North America to invest in another MDM or MAM-based security solution. For example, BYOD security solutions are very important in large organizations that are highly dependent upon using them like Microsoft and Google, which rely on these solutions to manage how personal devices are used by employees and other personnel at their organizations, and ensure they meet their security standards.
Asia Pacific is projected to grow at the fastest CAGR during 2024 to 2032. Such growth is fueled by the speedy digital transformation that is occurring in the region, the rise in the usage of mobile devices, and the developing mobile market of the nations in the region. There is a growing acceptance of mobile device usage across Asia, especially in India and China, and businesses are transitioning into the mobile-first economy. The increasing SMEs in the region will further boost demand for affordable and scalable BYOD security solutions. Realistically, the likes of Tencent (China) and Samsung Electronics (South Korea) have already embraced mobile technologies and line-of-business processing through consumerization and become ripe for BYOD security guarding their inevitably expanding digital environments.
Key players
Some of the major players in the BYOD Security Market are:
-
IBM (IBM MaaS360, IBM Security Identity Governance)
-
Citrix Systems (Citrix Endpoint Management, Citrix Secure Workspace Access)
-
Good Technology (BlackBerry) (Good Work, Good for Enterprise)
-
MobileIron (MobileIron Unified Endpoint Management, MobileIron Cloud)
-
VMware (VMware Workspace ONE, VMware AirWatch)
-
Fortinet (FortiMobile, FortiAuthenticator)
-
Cisco Systems (Cisco Meraki Systems Manager, Cisco Identity Services Engine)
-
Avaya (Avaya Device Management, Avaya Cloud Office)
-
Hewlett Packard Enterprise (HPE Aruba ClearPass, HPE Secure Networking)
-
Symantec (Broadcom) (Symantec Endpoint Protection, Symantec Mobile Management)
-
McAfee (McAfee Complete Endpoint Protection, McAfee Enterprise Mobility Management)
-
Kaspersky (Kaspersky Endpoint Security, Kaspersky Mobile Security)
-
Trend Micro (Trend Micro Mobile Security, Trend Micro Enterprise Mobility Management)
-
Sophos (Sophos Mobile, Sophos Endpoint Protection)
-
Webroot (Webroot SecureAnywhere, Webroot Mobile Security)
-
Zimperium (Zimperium Mobile Threat Defense, Zimperium Mobile Security)
-
Palo Alto Networks (Palo Alto Networks Prisma Access, Palo Alto Networks GlobalProtect)
-
Qualcomm (Qualcomm Mobile Security, Qualcomm Secure Processing Unit)
-
Intel (Intel vPro Technology, Intel Security Essentials)
-
Zscaler (Zscaler Private Access, Zscaler Internet Access)
Some of the Raw Material Suppliers for BYOD Security Companies:
-
Qualcomm
-
Intel
-
Broadcom
-
NVIDIA
-
Samsung Electronics
-
Texas Instruments
-
Microchip Technology
-
Maxim Integrated
-
MediaTek
-
Advanced Micro Devices (AMD)
Get Customized Report as per Your Business Requirement - Request For Customized Report
RECENT TRENDS
-
In June 2024, Fortinet announced its acquisition of Lacework, a cloud security leader, to enhance its AI-driven cloud-native security platform, and strengthen Fortinet's capabilities in cloud infrastructure protection.
-
In November 2024, HP Inc. launched the HP Enterprise Security Edition, a suite of security features designed to protect business PCs from physical attacks. The solution offers multilayered safeguards and enhanced visibility for IT admins to detect tampering with hardware and firmware.
-
In May 2024, Palo Alto Networks launched Prisma SASE 3.0, enhancing security with Zero Trust and AI-powered data protection, alongside App Acceleration for faster app performance.
Citrix Systems -Company Financial Analysis
| Report Attributes | Details |
|---|---|
|
Market Size in 2023 |
USD 61.5 Billion |
|
Market Size by 2032 |
USD 209.19 Billion |
|
CAGR |
CAGR of 14.61% From 2024 to 2032 |
|
Base Year |
2023 |
|
Forecast Period |
2024-2032 |
|
Historical Data |
2020-2022 |
|
Report Scope & Coverage |
Market Size, Segments Analysis, Competitive Landscape, Regional Analysis, DROC & SWOT Analysis, Forecast Outlook |
|
Key Segments |
• By Device Type (Laptop, Smart Phone, Tablet) |
|
Regional Analysis/Coverage |
North America (US, Canada, Mexico), Europe (Eastern Europe [Poland, Romania, Hungary, Turkey, Rest of Eastern Europe] Western Europe] Germany, France, UK, Italy, Spain, Netherlands, Switzerland, Austria, Rest of Western Europe]), Asia Pacific (China, India, Japan, South Korea, Vietnam, Singapore, Australia, Rest of Asia Pacific), Middle East & Africa (Middle East [UAE, Egypt, Saudi Arabia, Qatar, Rest of Middle East], Africa [Nigeria, South Africa, Rest of Africa], Latin America (Brazil, Argentina, Colombia, Rest of Latin America) |
|
Company Profiles |
IBM, Citrix Systems, Good Technology (BlackBerry), MobileIron, VMware, Fortinet, Cisco Systems, Avaya, Hewlett Packard Enterprise, Symantec (Broadcom), McAfee, Kaspersky, Trend Micro, Sophos, Webroot, Zimperium, Palo Alto Networks, Qualcomm, Intel, Zscaler. |
|
Key Drivers |
• Rising Cyber Threats and Increased Attacks Fueling the Need for Strong BYOD Security Solutions |
|
RESTRAINTS |
• Managing Device Diversity and User Negligence in BYOD Security Remains a Major Challenge for Enterprises |
Frequently Asked Questions
Ans: The BYOD Security Market is expected to grow at a CAGR of 14.61% during 2024-2032.
Ans: BYOD Security Market size was USD 61.5 billion in 2023 and is expected to Reach USD 209.19 billion by 2032.
Ans: The major growth factor of the BYOD Security Market is the rising adoption of remote work and mobile-first strategies, driving demand for robust solutions to secure personal devices accessing corporate networks.
Ans: The Mobile Device Management segment dominated the BYOD Security Market in 2023.
Ans: North America dominated the BYOD Security Market in 2023.

