Cybersecurity Market Size & Overview:

Get more information on Cybersecurity Market - Request Sample Report
Cybersecurity Market was valued at USD 195.1 billion in 2023 and is expected to reach USD 542.3 Billion by 2032, growing at a CAGR of 12.05% from 2024-2032.
The cybersecurity market is growing swiftly, due to the rise in the number and complexity of cyber threats, and digital transformation occurring at a fast pace across sectors. The reason for this growth is the increasing demand for security solutions with cloud computing, IoT, and AI technologies. The dramatic rise in cyber-attacks and data breaches is one of the main drivers of this growth. This proves the utmost importance of a stricter security process, especially in finance, healthcare, and retail industries.
Market growth is further propelled by the rapid shift to remote work and cloud computing due to the COVID-19 pandemic. The shift of enterprises to the cloud has triggered a massive surge in demand for sophisticated Security solutions like multi-factor authentication, end-to-end encryption, and secure access service edge (sase) frameworks. Leading cloud providers such as Microsoft and Google are now embedding their platforms with advanced security functionalities to ensure that user data is well governed and meets compliance obligations such as the Rajon-General Data Protection Regulation (GDPR) and California Consumer Privacy Act (CCPA). Moreover, the rising sophistication of cybercrime and a rise in demand for sophisticated threat detection technologies have given rise to AI-based cybersecurity solutions. However, Palo Alto Networks reported that demand for its AI-based threat detection services rose 30% in 2023, illustrating the increasing need for reliance on AI services to proactively identify threats and respond to them. With organizations experiencing increased pressure to protect sensitive data, the market for cybersecurity solutions such as firewalls, intrusion detection systems (IDS), and endpoint security tools is rising. This trend is further driven by the increasing compliance requirements for regulatory compliance, which motivates organizations to utilize these advanced technologies for securing their digital assets and thus avoiding costly penalties.
|
Industry |
Company/Organization |
Cybersecurity Investment Focus |
|---|---|---|
|
Financial |
JP Morgan Chase |
$600 million annually on cybersecurity infrastructure |
|
Healthcare |
Anthem Inc. |
Increased investment in ransomware defense and patient data security |
|
Retail |
Walmart |
Strengthening e-commerce security through AI-driven fraud detection |
|
Technology |
|
Advanced cloud security and endpoint protection tools for cloud services |
Cybersecurity Market Dynamics
Drivers
-
The rising frequency and sophistication of cyber-attacks are creating a higher demand for advanced cybersecurity solutions to protect sensitive data and networks.
-
High-profile data breaches and growing concerns over data privacy are propelling businesses to invest in robust security measures.
-
As businesses increasingly adopt digital technologies such as AI, IoT, and big data, the need for comprehensive cybersecurity solutions grows to safeguard complex infrastructures.
The rapid digitalization of businesses across sectors via technologies such as artificial intelligence (AI), the Internet of Things (IoT), and big data has resulted in such vastness and complexity of IT infrastructures, which consequently gives rise to an extensive need for swift, holistic cybersecurity. These technologies assist organizations with increased operational efficiency, improve user experiences, and be insightful from massive data. But, they also bring new security risks that need to be controlled to safeguard sensitive information and maintain business continuity.
For example, the automation of decision-making processes and the improvement of prediction capabilities brought by AI also has its benefits. However, it also introduces new security concerns such as algorithmic manipulation and adversarial attacks that can compromise system integrity. Likewise, the increase in Internet of Things (IoT) devices from consumer smart devices to industrial sensors is another factor widening the attack surface with more entry points available to cybercriminals. Most of these gadgets do not have solid warranties — which increases the risk of data breaches and cyber-attacks. The sudden growth of IoT, especially concerning healthcare, manufacturing, and logistics has paved the way for the need for specialty security solutions for these interconnected systems.
Big data has changed how industries operate, allowing organizations to make data-driven decisions based on a massive amount of data. Yet, the security challenges posed by BIG data are exacerbated by its volume and complexity, making it more attractive to criminals, and rendering huge amounts of data open to theft and ransom. Ensuring integrity, confidentiality, and compliance with big data (and stringent regulations like GDPR) are key motivators of investment dollars in next-gen cybersecurity solutions.
To tackle these enormous challenges, businesses are adopting all-in-one cybersecurity plans that incorporate AI-based threat detection, real-time monitoring, advanced encryption, and a safe cloud infrastructure. These solutions enable heightened management of the increasing complexity digital environments facilitate and a complex threat landscape. The cybersecurity market is growing in light of the increasing need for enhanced protection and regulatory compliance.
Restraints
-
Many SMEs lack the financial resources to implement advanced cybersecurity solutions, which makes them more vulnerable to cyberattacks
-
Organizations often face internal resistance to adopting new security technologies or shifting from legacy systems to more advanced cybersecurity solutions, delaying necessary upgrades
-
The sheer volume of security data generated can overwhelm security teams, leading to missed threats or delayed responses, reducing the effectiveness of security systems
Modern IT environments result in a substantial amount of security data, making it difficult for cybersecurity teams to manage trends. With tools such as firewalls, IDS, IPS, and endpoint protection solutions playing a vital role in detecting vulnerabilities and cyber threats, organizations realize they are generating an overwhelming amount of data in the form of logs, alerts, and traffic analysis. Consequently, it makes it difficult for the security analyst to prioritize alerts and often causes a threat to be missed or a delayed response. In addition to being resource-intensive, automated systems can create many alerts at once, most of which can be false positives, making it difficult for analysts to determine what cyber threats are in real time. The inability to address these alerts promptly leaves the systems open to attacks of ransomware, phishing, or data exfiltration, with studies showing that security teams do not have the bandwidth to investigate alerts immediately and that a delay in remediating attacks is possible.
The situation is further exacerbated by the rapid expansion of connected devices, networks, and cloud infrastructure, which adds complexity to the management of security data. Without the proper tools in place to aggregate and analyze data, detecting and responding to threats becomes a more challenging task. This is especially true for the small and medium-sized enterprises (SMEs) that do not have the resource base to implement solutions like Security Information and Event Management (SIEM) systems or AI-based threat detection tools as these can help reduce demands on data analysis resources by filtering through threats to focus on those that are critical.
Cybersecurity Market Segmentation Analysis
By Organization Size
In 2023, the largest enterprise segment dominated the market and accounted for the highest share of revenue at 69.7%. Market drivers include large enterprise spending on IT infrastructure to enhance digital security to ensure the protection of large data storage. In addition, large enterprises have many servers, storage devices, endpoints & networks which can cause huge financial impacts due to cyber-attacks. Larger enterprises are focusing on the deployment of cyber security solutions to not only manage such issues but to secure the data fuelling the growth of the market.
The SME segment is projected to witness the fastest CAGR of 14.1% during the forecast period. SMEs are facing a greater challenge because of the pandemic, but their low-security postures make them more susceptible to attack, especially if cost savings have to be made. Also, their vacancy of security policies and worker skills additionally pulls them due to the very nature of a cyber-attack. Due to the aforementioned challenges, SMEs opt for cyber security insurance which shields them from financial losses from malicious software attacks and data breaches and aids the growth of this segment.
By Deployment
On-premises segment accounted for the largest market share of 62.8% in 2023 and will dominate the market over the forecast period. Complete ownership of the solutions by large enterprises ensures that the data is secure at an optimum level, due to the growing segment. In addition, on-premise security solutions further decrease the reliance on third-party companies surveying and securing data.
The cloud segment is expected to grow at a CAGR of 12.8% over the forecast period. This skyrocketing growth comes from migrating from the on-premises solutions of enterprises to the cloud. In addition, the cost and ease of deployment & management of cloud-based solutions are billowing the growth of this segment. Also, the reach for the solutions accessible over the devices in cloud technology is expected to create a lucrative opportunity for the growth of this segment.
By Component
The solutions segment dominated the market and represented a significant revenue share of 63.8%, with cyberattacks on the rise throughout recent years — from ransomware and phishing to data breaches — companies are spending a lot of money on proactive security. Cloud security solutions are in high demand because everyone is moving to the cloud so fast. As hybrid and multi-cloud environments rise, organizations are searching for solutions to protect and comply with data. As cyber threats become ever more sophisticated, so too will the solutions evolve; integrating AI and ML for faster detection and response capabilities. The specific market drivers are expected to continue to be driven by endpoint protection solutions and cloud security solutions considering the need for secure remote work. The increasing number of IoT devices also drives better protection will further lead to enable demand for integrated cybersecurity solutions.
The Services segment is expected to grow at the highest CAGR during the forecast period. Includes managed security services, incident response, security consulting, and training services. Organizations are struggling to fulfill the ever-evolving security needs, thanks to the rise in cyber threats and the explosion of complexity in IT environments. As a result, organizations use third-party specialized service providers for cyber security. The remote work boom, combined with more complex multi-cloud and hybrid environments, continues to drive demand for managed security services providers (MSSPs) for 24x7 monitoring, threat detection, and incident response. Increased demand for regulatory compliance — With the expansion of data protection laws like GDPR, HIPAA, etc., the need for regulatory compliance has never been higher, especially in sectors like healthcare, finance, and government, in turn increasing the demand for cybersecurity services.
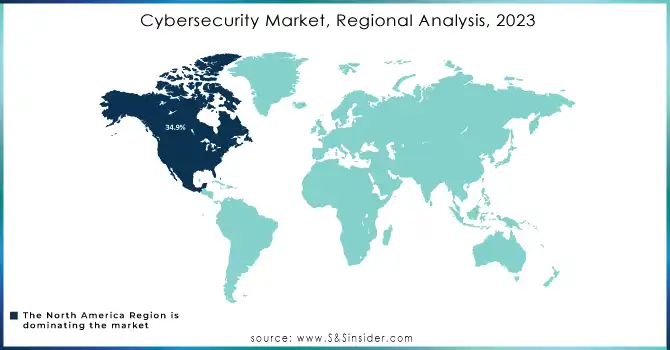
Regional Analysis
In 2022, North America dominated the market and accounted for the largest market share of 34.9%. North America's cyber security market is growing steadily as with some of the latest technologies it is been continued developed such as big data and the Internet of Things (IoT). In addition, the increasing number of IT companies and their diversified businesses in the region is prompting the requirement for endpoint device protection. In addition, governments around the world continue to pursue different initiatives to increase cyber security awareness in organizations and to promote and assist organizations to adopt sufficient cyber security measures. So, these above factors are going to drive the North American cyber security market.
Asia Pacific is projected to grow at the fastest CAGR throughout the forecast period. A growing number of data centers, increasing adoption of cloud technologies, growing cyber security jobs, and proliferation of IoT devices are attributing to the growth of the Asia Pacific cyber security market. In addition to this, various organizations in the Asia cyber security market solutions have inbuilt features to spot any possible weaknesses this is also shown as a supportive scenario for Asia Pacific cyber security market growth.
Need any customization research on Cybersecurity Market - Enquiry Now
Key Players
The major key players along with their products are
-
Cisco Systems - Cisco SecureX
-
Palo Alto Networks - Prisma Cloud
-
Check Point Software - Quantum Security Gateway
-
IBM Corporation - QRadar SIEM
-
Fortinet - FortiGate Firewall
-
McAfee - McAfee Endpoint Security
-
Symantec (Broadcom) - Symantec Endpoint Protection
-
Trend Micro - Trend Micro Apex One
-
Splunk - Splunk Enterprise Security
-
FireEye (Trellix) - Helix Security Platform
-
Sophos - Sophos Intercept X
-
CrowdStrike - CrowdStrike Falcon
-
Proofpoint - Proofpoint Email Protection
-
Forcepoint - Forcepoint DLP
-
Zscaler - Zscaler Internet Access
-
Okta - Okta Identity Management
-
Qualys - Qualys Cloud Platform
-
Bitdefender - Bitdefender GravityZone
-
Darktrace - Darktrace Cyber AI
-
Kaspersky Lab - Kaspersky Total Security
Recent Developments
January 2024: Palo Alto Networks Launched an AI-powered platform to automate threat detection and response for cloud-native environments
February 2024: CrowdStrike Introduced new endpoint detection capabilities with enhanced cloud integration to counter advanced persistent threats (APTs)
March 2024: Gem Security and Avalor both companies were acquired for $350 million each, focusing on threat detection and security analytics
| Report Attributes | Details |
| Market Size in 2023 | USD 195.1 billion |
| Market Size by 2032 | USD 542.3 Billion |
| CAGR | CAGR of 12.05% from 2024-2032. |
| Base Year | 2023 |
| Forecast Period | 2024-2032 |
| Historical Data | 2020-2022 |
| Report Scope & Coverage | Market Size, Segments Analysis, Competitive Landscape, Regional Analysis, DROC & SWOT Analysis, Forecast Outlook |
| Key Segments |
• By Offering (Solution, Services) |
| Regional Analysis/Coverage | North America (US, Canada, Mexico), Europe (Eastern Europe [Poland, Romania, Hungary, Turkey, Rest of Eastern Europe] Western Europe] Germany, France, UK, Italy, Spain, Netherlands, Switzerland, Austria, Rest of Western Europe]), Asia Pacific (China, India, Japan, South Korea, Vietnam, Singapore, Australia, Rest of Asia Pacific), Middle East & Africa (Middle East [UAE, Egypt, Saudi Arabia, Qatar, Rest of Middle East], Africa [Nigeria, South Africa, Rest of Africa], Latin America (Brazil, Argentina, Colombia, Rest of Latin America) |
| Company Profiles |
Cisco Systems, Palo Alto Networks, Check Point Software, IBM Corporation, Fortinet, McAfee, Symantec (Broadcom), Trend Micro, Splunk, FireEye, Sophos, CrowdStrike, Proofpoint, Forcepoint |
| Key Drivers | •The rising frequency and sophistication of cyber-attacks are creating a higher demand for advanced cybersecurity solutions to protect sensitive data and networks. •High-profile data breaches and growing concerns over data privacy are propelling businesses to invest in robust security measures. •As businesses increasingly adopt digital technologies such as AI, IoT, and big data, the need for comprehensive cybersecurity solutions grows to safeguard complex infrastructures. |
| Market Opportunities | •Many SMEs lack the financial resources to implement advanced cybersecurity solutions, which makes them more vulnerable to cyberattacks •Organizations often face internal resistance to adopting new security technologies or shifting from legacy systems to more advanced cybersecurity solutions, delaying necessary upgrades •The sheer volume of security data generated can overwhelm security teams, leading to missed threats or delayed responses, reducing the effectiveness of security systems |

