Health IT Security Market Report Scope & Overview:
The Health IT Security Market Size was valued at USD 15.3 billion in 2023 and is expected to reach USD 53.9 billion by 2032 and grow at a CAGR of 15.04% over the forecast period 2024-2032.
Growth prospects in the health IT security market are enormous in the future years and are primarily driven by the ever-escalating need for healthcare organizations to combat cybercrime. Hospital and healthcare facility operations are widely threatened by cybercriminals who have often exploited software complexity and devices to gain unauthorized access to delicate sensitive data. It is interesting to note that data breaches occur quite often in conjunction with the misapplication of highly secured information. Therefore, the health IT system demands an effective policy to control the security breach. The cost to the economy of such data breaches is hefty, and this has made healthcare entities in all geographies invest heavily in protection against cyber threats.

Get more information on Health IT Security Market - Request Sample Report
This is a growing market lately, going forward due to digitization of healthcare systems, rising cyberattacks, and tightening regulations. Health organizations increasingly realize that the protection of patient data is fundamental to maintaining confidentiality, integrity, and availability. Electronic health records, telemedicine, and connected medical devices have increased the volume of demand for robust IT security solutions exponentially.
Importantly, investment in health IT security is driven by regulatory compliance. HIPAA in the United States and GDPR in Europe put strict standards for security measures on healthcare companies. Being non-compliant may lead to large fines and reputational loss and drive healthcare providers to invest in security solutions for IT so that health organizations can meet these regulations to protect the sensitive information of patients. The COVID-19 pandemic has increased the consumption of telehealth services even more rapidly. This accelerated growth has brought new cybersecurity issues. Increased virtual consultations and remote monitoring have ushered in growing new threats of cyberattacks that call for health IT security technologies increased investments.
Health IT security encompasses the protection of electronic health records, information related to the health of patients, medical equipment, and telehealth systems from data breaches and unauthorized access. With growing concerns over patient information, personal health information safeguarding requires more security solutions. The requirements of safety and security in achieving regulated standards have resulted in a high demand for integrated solutions of connected medical devices and advanced healthcare IT. A close regulation by the government has increased its demand for developing efficient health IT security strategies.
Table 1: Healthcare Data Protection Regulations Impacting Health IT Security
|
Region |
Key Regulation |
Description |
|---|---|---|
|
United States |
Health Insurance Portability and Accountability Act (HIPAA) |
Governs the protection of patient health information |
|
European Union |
General Data Protection Regulation (GDPR) |
Mandates data protection and privacy for all individuals |
|
Canada |
Personal Information Protection and Electronic Documents Act (PIPEDA) |
Protects personal information in healthcare |
|
Australia |
Privacy Act 1988 |
Ensures data privacy and patient confidentiality |
|
Japan |
Act on the Protection of Personal Information (APPI) |
Regulates the handling of personal health data |
Table 2: Health IT Security Solutions by Key Players
|
Company Name |
Security Solution/Product |
Target Application/Feature |
|---|---|---|
|
Cisco Systems, Inc. |
Cisco Secure Firewall |
Network protection, threat detection |
|
Palo Alto Networks |
Cortex XDR |
Endpoint detection and response, threat intelligence |
|
IBM Corporation |
IBM Security QRadar SIEM |
Threat detection, compliance management |
|
McAfee, LLC |
McAfee Total Protection |
Endpoint protection, malware detection |
|
Symantec Corporation |
Symantec Endpoint Security |
Endpoint detection, cloud security |
Health IT Security Market Dynamics
Drivers
-
Rising Breaches and Cloud Adoption Demand Robust Cybersecurity Solutions for Healthcare
The health IT security market is growing at a relatively aggressive rate driven primarily by the skyrocketing incidence of cyberattacks against healthcare providers in North America and Europe. According to the American Medical Association, over 3.34 million healthcare records were compromised in the U.S. each month from July 2020 to June 2021 due to ransomware and other forms of cyber threats. This often-stolen data contains the confidential information of patients, and it is sold at a good price. For instance, the $67 million loss of Universal Health Services owing to ransomware attacks.
Another prominent factor driving demand in the market is the growth of cloud computing. Cloud technology is rapidly being viewed by healthcare organizations as a means to optimize workflows and decrease costs for better operations efficiency. With an increasing rise in telehealth services, this necessity widens further as 76% of U.S. hospitals used telemedicine in 2020. The shift towards these services requires effective IT security solutions that can be established to protect cloud-based systems against cyber threats.
The rapidly expanding number of connected medical devices, especially those under the IoMT, expands the attack surface for cybercriminals. Securing such devices is important not just for patient safety but in maintaining data integrity. In health organizations where the stricter the regulations are about keeping a patient's privacy, the more they will require sophisticated health IT security solutions to be in place to effectively prevent unauthorized access and data breaches.
Restraints
-
Limited Availability of Skilled Professionals
The presence of a shortage of specialists in cybersecurity, particularly the personnel who are well-versed with specific issues in security concerned with health, hinders the recruitment of competent personnel and their retention in healthcare organizations which compromises the implementation and maintenance of appropriate measures for security.
-
Compliance and Resource Constraints
Health IT Security Market - Key Segmentation
by Products and Services
Products dominated the health IT security market in 2023 with a 57.3% share, which is the primary backbone for protecting sensitive patient information. Among the products are firewalls, antivirus software, and intrusion detection systems that prevent ransomware and data breaches on healthcare networks and beyond, including data cyber threats. As healthcare institutions transition towards more digital systems and cloud-based services, the demand for these products grows. Innovations in artificial intelligence and machine learning only elevate the levels of functionality of security software, which can automatically detect and respond to threats in real time while cyberattacks are on the rise.
On the other hand, services are the fastest-growing sector of health IT security. It is difficult for most healthcare organizations to identify the appropriate cybersecurity personnel; thus, most of them outsource to firms that deal with security needs. Among the managed services are continuous monitoring, threat detection, incident response, and compliance management. These services provide comprehensive solutions that shore up cybersecurity defenses. This trend is more apparent among smaller healthcare facilities looking for ways to ensure security without using up limited resources.
by Application
Network security was the dominant application area of health IT security with a 37.6% share in 2023. It is the backbone of an effective cybersecurity strategy in any organization. Organizations have increased efforts in securing their infrastructure with minimal risks of unauthorized access, breach of confidential data, and even ransomware attacks. This has included the provision of a series of firewall systems, VPN, and intrusion prevention mechanisms aiming to protect confidential information related to patients across transmissions. As telehealth and cloud solutions are rolled into the healthcare industry, attention to network security is heightened to ensure patient data is properly secured on a broad spectrum and channel.
Endpoint security is the fastest-growing application area, up from last year due to the high degree of penetration of medical devices and remote work arrangements within the healthcare industry. The more endpoints - for example, laptops, cell phones, and IoMT devices - the more there will be created with points of weakness as the device connects to healthcare networks. They focus on endpoint protection as these devices present vulnerabilities; therefore, they use antivirus software, endpoint detection and response, as well as mobile device management. Telehealth services have increased as medical professionals have to access networks safely from various locations.
by Delivery Mode
The on-premise solutions dominated the delivery mode segment for health IT security with a 59.3% share in 2023, mainly among the larger healthcare organizations that worried themselves over control over their security infrastructure. Such systems allow customization and integration with the current infrastructure of the already existing IT frameworks and can ensure a sense of security for sensitive patient data stored onsite. It remains that the organization seeks this model primarily due to its perceived reliability and direct control, especially in an environment where regulatory compliance is key.
The fastest growing delivery mode is on-demand solutions, since more healthcare organizations and facilities increasingly adopt cloud-based services. This model offers scale, flexibility, and the ability to access such services based on organizational requirements, with no up-front cost for potentially obsolete infrastructure. As telehealth and remote patient monitoring are increasingly adopted in healthcare, the demand for on-demand security solutions is becoming ever higher to secure diverse data sets across various devices and locations. This trend is further fueled by the need for organizations to respond swiftly to evolving cyber threats while being effective in the management of limited IT resources.
by End User
The health care providers held the largest end-user segment in the health IT security market in 2023 with a 54.5% share. Healthcare providers deal with massive patient data, hence requiring strong safety measures to be deployed. Thus, hospitals, clinics, and other healthcare facilities pay much attention to cybersecurity solutions that can protect their data from cyber-attacks and adhere to regulations like HIPAA. The growing adoption of EHRs and telemedicine solutions generates greater pressure on healthcare providers to invest in sophisticated security measures to protect their systems and patient trust.
Healthcare payers are the fastest-growing end-user segment since insurance companies and managed care organizations are still finding the need for high-level security solutions to protect patient data and ensure regulatory compliance. That the vast majority of the payers are going to rely on digital health solutions and electronic transactions seriously puts sensitive information at risk of cyber threats. Consequently, this implies a higher demand to implement advanced security measures to deter data breaches and fraud, and customized security services are needed in this segment to meet the requirement.
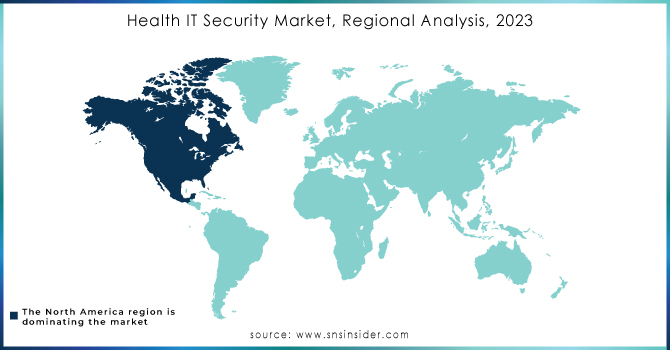
Health IT Security Market Regional Analysis
North America emerged as the leading region in the health IT security market in 2023 with a 48.2% share, with the United States taking a major portion of the overall market share. This can be attributed to a robust healthcare infrastructure, high investment in advanced security technologies, and stringent regulatory frameworks that focus on safeguarding sensitive patient data. The growing incidents of cyber-attacks reported in this region have furthered the focus of healthcare IT on effective health security measures.
On the other hand, the market in Asia is expected to grow at the highest compound annual growth rate (CAGR) over the forecast period. The reason mainly lies in increasing IT security awareness among healthcare providers and the general public. Government initiatives in enforcing stringent data security regulations also form a significant part of the growth. Demand for effective health IT security solutions is further being fueled by the overall adoption of mobile devices within healthcare practices. With the sensitive patient information that needs to be protected in this context of digital transformation, the Asia-Pacific region is expected to witness much more development in health IT security and, therefore, forms an important space for market players to focus on.
Need any customization research on Health IT Security Market - Enquiry Now
Key Players
-
Citrix Systems, Inc.
-
Juniper Networks, Inc.
-
Forescout Technologies, Inc.
-
Cisco Systems, Inc.
-
Symantec Corporation
-
McAfee, LLC
-
Trend Micro, Inc.
-
Palo Alto Networks, Inc.
-
Sophos Group plc
-
Proofpoint, Inc.
-
Fortinet, Inc.
-
FireEye, Inc.
-
Forcepoint LLC
-
Cerner Corporation
-
Microsoft Corporation
-
Check Point Software Technologies Ltd.
-
Allscripts Healthcare Solutions, Inc. and others.
Recent Developments
April 2024 - Fortified Health Security released its 2024 Horizon Report, emphasizing the urgent need for healthcare organizations to bolster their cybersecurity measures. The report highlights a substantial rise in compromised patient records and the critical importance of Third-Party Risk Management (TPRM) due to increased breaches reported by Business Associates. It also discusses the integration of AI and machine learning in enhancing healthcare cybersecurity.
March 2024 - Palo Alto Networks announced an upgraded security platform designed specifically for the healthcare sector. This platform aims to simplify the complexities associated with managing multiple security products by consolidating functionalities. The focus is on securing connected medical devices and simplifying the security landscape for healthcare providers.
February 2024 - IBM Security unveiled new AI-driven solutions aimed at enhancing healthcare cybersecurity. These solutions are designed to automate threat detection and response processes, enabling healthcare organizations to manage cyber threats more effectively.
| Report Attributes | Details |
|---|---|
| Market Size in 2023 | USD 15.3 Billion |
| Market Size by 2032 | USD 53.9 Billion |
| CAGR | CAGR of 15.04% From 2024 to 2032 |
| Base Year | 2023 |
| Forecast Period | 2024-2032 |
| Historical Data | 2020-2022 |
| Report Scope & Coverage | Market Size, Segments Analysis, Competitive Landscape, Regional Analysis, DROC & SWOT Analysis, Forecast Outlook |
| Key Segments | • By Products and Services (Products, Services) • By Application (Network Security, Endpoint Security, Application Security, Content Security) • By Delivery Mode (On-premise, On-demand) • By End User (Healthcare Providers, Healthcare Payers) |
| Regional Analysis/Coverage | North America (US, Canada, Mexico), Europe (Eastern Europe [Poland, Romania, Hungary, Turkey, Rest of Eastern Europe] Western Europe] Germany, France, UK, Italy, Spain, Netherlands, Switzerland, Austria, Rest of Western Europe]), Asia-Pacific (China, India, Japan, South Korea, Vietnam, Singapore, Australia, Rest of Asia-Pacific), Middle East & Africa (Middle East [UAE, Egypt, Saudi Arabia, Qatar, Rest of Middle East], Africa [Nigeria, South Africa, Rest of Africa], Latin America (Brazil, Argentina, Colombia, Rest of Latin America) |
| Company Profiles | Citrix Systems, Inc., Juniper Networks, Inc., Forescout Technologies, Inc., IBM Corporation, Cisco Systems, Inc., Symantec Corporation, McAfee, LLC, Trend Micro, Inc., Palo Alto Networks, Inc., Sophos Group plc, Proofpoint, Inc., Fortinet, Inc., FireEye, Inc., Forcepoint LLC, Cerner Corporation, Oracle Corporation, Microsoft Corporation, Dell Technologies, Inc., Check Point Software Technologies Ltd., Allscripts Healthcare Solutions, Inc. and Others |
| Key Drivers | • Rising Breaches and Cloud Adoption Demand Robust Cybersecurity Solutions for Healthcare |
| Restraints | • Limited Availability of Skilled Professionals • Compliance and Resource Constraints |
Frequently Asked Questions
The Development of Future IT Security Solutions, New Growth Paths Provided by Cloud Security are the opportunities of Health IT Security Market.
The by Application is divided into four sub segments is Network Security, Endpoint Security, Application Security, and Content Security.
The challenges faced by Health IT Security market is Cyberattacks with Frequently Varying Nature
Ans: The Health IT Security Market is growing at a CAGR of 15.04% over the forecast period 2024-2032.
Ans: The Health IT Security Market size estimated to reach USD 53.9 billion by 2032.

